Welcome to “Naijaclass Academy” For Neco 2024 Computer Studies Answer (June/July Exam)

Date: Thursday, 27th June 2024
Computer Studies (Objective & Essay) 2:00pm – 5:00pm.
——————————
COMPUTER STUDIES
1-10: AAADDBBBCC
11-20: CDBDCBDACD
21-30: DEAECBBEAA
31-40: EDACDBACAC
41-50: ADDADBEBAB
51-60: AEEEAECACE
NUMBER 1
(1a)
The concept of a database refers to an organized collection of structured data that is stored and managed electronically. It is designed to efficiently store, retrieve, and manage large amounts of information. Databases typically use tables to organize data into rows and columns.
(1bi)
Character: A character is a single text unit or symbol, such as a letter, number, punctuation mark, or space.
(1bii)
Field: In database terminology, a field is a specific type of data stored in a table. A field usually contains information relevant to the entire row of data that it belongs to.
(1c)
(PICK ANY TWO)
(i) Access to information: The internet provides access to a huge amount of information that would otherwise be unavailable.
(ii) Communication: The internet has revolutionized how we communicate with one another. People can exchange messages instantly and communicate in real-time, no matter where they are located.
(iii) Entertainment: The internet has made it easier for people to access entertainment, such as movies, music, games, and much more.
(iv) Shopping: People can now shop online from anywhere in the world, without having to set foot inside a store.
(v) Social Networking: Sites like Facebook, Twitter, and LinkedIn provide a platform for people to share ideas and stay connected.
(vi) Education: The internet has made it easier than ever for students to learn, by providing access to an abundance of educational resources.
(1d)
A file is a collection of data that is stored on a computer or other electronic device. It can contain text, images, videos, programs, or any other type of information. Files are typically named and have a specific file format that determines how the data should be organized.
WHILE
A folder is a virtual container in a computer’s file system that stores and organizes multiple files. Folders allow users to logically group related files together, making it easier to locate them when needed.
====================
NUMBER 2
(2ai)
-Bus Topology-
A bus topology is a network configuration where all the devices are connected to a single communication line, called a bus. In this topology, devices are connected to the bus through a device that acts as a repeater, allowing the signal to be propagated in both directions.
(2aii)
-Star Topology-
A star topology is a network configuration in which each device is connected directly to a single central device known as the “hub”. In this topology, the hub acts as a connection point between all the other devices in the network and sends data packets to each device.
(2bi)
Hacking: Hacking is the unauthorized access or control of another person’s computer system in order to steal or manipulate data or resources.
(2bii)
Piracy: Piracy is the unauthorized copying or distribution of copyrighted material such as music, movies, software, etc.
(2c)
(i) Hard Disk Drives (HDDs): These are traditional storage devices that use magnetic discs to store and retrieve data. *Examples* Western Digital Caviar Blue, Seagate BarraCuda
(ii) Solid-State Drives (SSDs): These are newer storage devices that use integrated circuits to store and retrieve data. *Examples* the Samsung 860 EVO, Kingston A400.
====================
NUMBER 3
(3ai)
An operating system is a software that manages computer hardware and software resources and provides common services for computer programs.
(3aii)
(i) Windows Operating System
(ii) Linux Operating System
(3bi)
(PICK ANY TWO)
(i) To provide uninterrupted power supply.
(ii) To ensure data security.
(iii) To prevent system crashes due to electricity failure.
(iv) To provide protection against power surges.
(v) To protect data from corruption.
(vi) To keep the system running in case of an emergency.
(3bii)
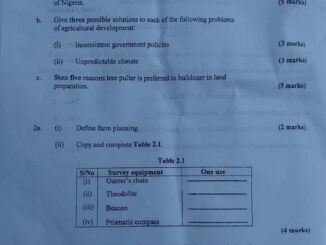
(DIAGRAM)
(3biii)
The octal number system is based on the base 8 system, with the numbers 0 to 7 as its components, WHILE the binary number system is based on the base 2 system, with the numbers 0 and 1 as its components.
(3biv)
(i) Portrait Orientation
(ii) Landscape Orientation
====================
(4a)
(i) Videoconference:
Videoconferencing allows people in different locations to hold face-to-face meetings without having to move to a single location physically. It is widely used for business meetings, distance education, and medical consultations. Participants can see and hear each other in real-time through video and audio communication, share documents, and collaborate effectively.
(ii) Telepresence:
Telepresence refers to technologies that allow a person to feel as if they were present at a location other than their true location. It often involves sophisticated video conferencing equipment that provides high-definition video and audio, making it seem like participants are in the same room. Telepresence aims to create a more immersive and realistic interaction, enhancing remote communication.
(iii) Teleconference:
Teleconferencing is a telephone meeting among two or more participants involving technology more sophisticated than a simple two-way phone connection. It may involve audio, video, and data sharing. Teleconferencing is used for business meetings, training sessions, and seminars, enabling people to connect and collaborate without the need for physical travel.
(4b)
10 LET sum = 0
20 FOR i = 11 TO 50 STEP 2
30 LET sum = sum + i
40 NEXT i
50 PRINT “The sum of odd numbers from 11 to 50 is “; sum
60 END
==================================
(5ai)
Primary data is data collected directly from first-hand experience. This data is original and has not been previously published. In the other hand, Secondary data is data that has been previously collected and published by others. This data is not original but rather a summary or analysis of existing information.
(5aii)
(PICK ANY FOUR)
(i) Word Processing Software: Used for creating, editing, formatting, and printing documents. Examples include Microsoft Word and Google Docs.
(ii) Spreadsheet Software: Used for organizing, analyzing, and storing data in tabular form. Examples include Microsoft Excel and Google Sheets.
(iii) Database Management Software: Used for creating and managing databases. Examples include Oracle, MySQL, and Microsoft Access.
(iv) Presentation Software: Used for creating and displaying slideshows and presentations. Examples include Microsoft PowerPoint and Google Slides.
(v) Graphics and Design Software: Used for creating and editing visual content, including images, illustrations, and designs. Examples include Adobe Photoshop and CorelDRAW.
(vi) Web Browsers: Used for accessing and navigating the internet. Examples include Google Chrome, Mozilla Firefox, and Microsoft Edge.
(vii) Email Clients: Used for sending, receiving, and organizing emails. Examples include Microsoft Outlook and Mozilla Thunderbird
(5bi)
| A | B | C | D | Output (NAND) |
|—|—|—|—|—————|
| 0 | 0 | 0 | 0 | 1 |
| 0 | 0 | 0 | 1 | 1 |
| 0 | 0 | 1 | 0 | 1 |
| 0 | 0 | 1 | 1 | 1 |
| 0 | 1 | 0 | 0 | 1 |
| 0 | 1 | 0 | 1 | 1 |
| 0 | 1 | 1 | 0 | 1 |
| 0 | 1 | 1 | 1 | 1 |
| 1 | 0 | 0 | 0 | 1 |
| 1 | 0 | 0 | 1 | 1 |
| 1 | 0 | 1 | 0 | 1 |
| 1 | 0 | 1 | 1 | 1 |
| 1 | 1 | 0 | 0 | 1 |
| 1 | 1 | 0 | 1 | 1 |
| 1 | 1 | 1 | 0 | 1 |
| 1 | 1 | 1 | 1 | 0 |
(5bii)
(PICK ANY TWO)
(i) The Arithmetic and Logic Unit (ALU) performs all arithmetic operations such as addition, subtraction, multiplication, and division.
(ii) The ALU also performs logical operations such as AND, OR, NOT, XOR, and comparison operations (like equal to, greater than, and less than).
(iii) The ALU performs bitwise operations, which are operations that directly manipulate individual bits of binary numbers. These operations include bitwise AND, OR, XOR, and NOT.
(iv) The ALU can perform shift operations, which involve moving bits to the left or right within a binary number.
===========================
(6a)
(i)Register: A small amount of on-chip memory that stores data temporarily while it is being processed. Registers are the fastest memory locations and are used to store instructions, data, and addresses.
(ii)Clock: A timing device that generates a clock signal to synchronize the CPU’s operations. The clock speed measures the number of cycles per second.
(iii)Bus: A communication pathway that allows different components of the CPU to exchange data. Buses are used to connect registers, ALU, and other CPU components.
(6bi)
(i)Cyberbullying and online harassment, which can lead to mental health issues and social isolation.
(ii)Misinformation and disinformation, which can spread quickly and lead to confusion, mistrust, and harmful decisions.
(6bii)
(i)LAN (Local Area Network)
(ii)WAN (Wide Area Network)
(iii)MAN (Metropolitan Area Network)
(iv)WLAN (Wireless Local Area Network)


Am not on whatapp how are we going to do it.
I need the answer
Am not on whatapp how are we going to do it.
I need the answer
Polytechnic
Polytechnic
Am not wassapp how are we do
Okay
Am not wassapp how are we do
Okay
Abeg send chokes
Abeg send chokes
we still dey wait oooo
we still dey wait oooo
Duri bura
Duri bura
PLEASE SEND PHYSICS ANSWER FOR US
PLEASE SEND PHYSICS ANSWER FOR US